Shadow IT and Shadow AI: The Invisible Risks Threatening Your SME
Shadow IT refers to the unauthorized use of digital tools within a company — and its variant, Shadow AI, is now one of the main sources of data leaks for Swiss SMEs. Every time an employee copies customer data into ChatGPT or stores files on their personal Dropbox, your sensitive data escapes all control. Discover the concrete risks associated with the revised Federal Act on Data Protection (nLPD) and the American Cloud Act, and the sovereign solutions to regain control without hindering the productivity of your teams.
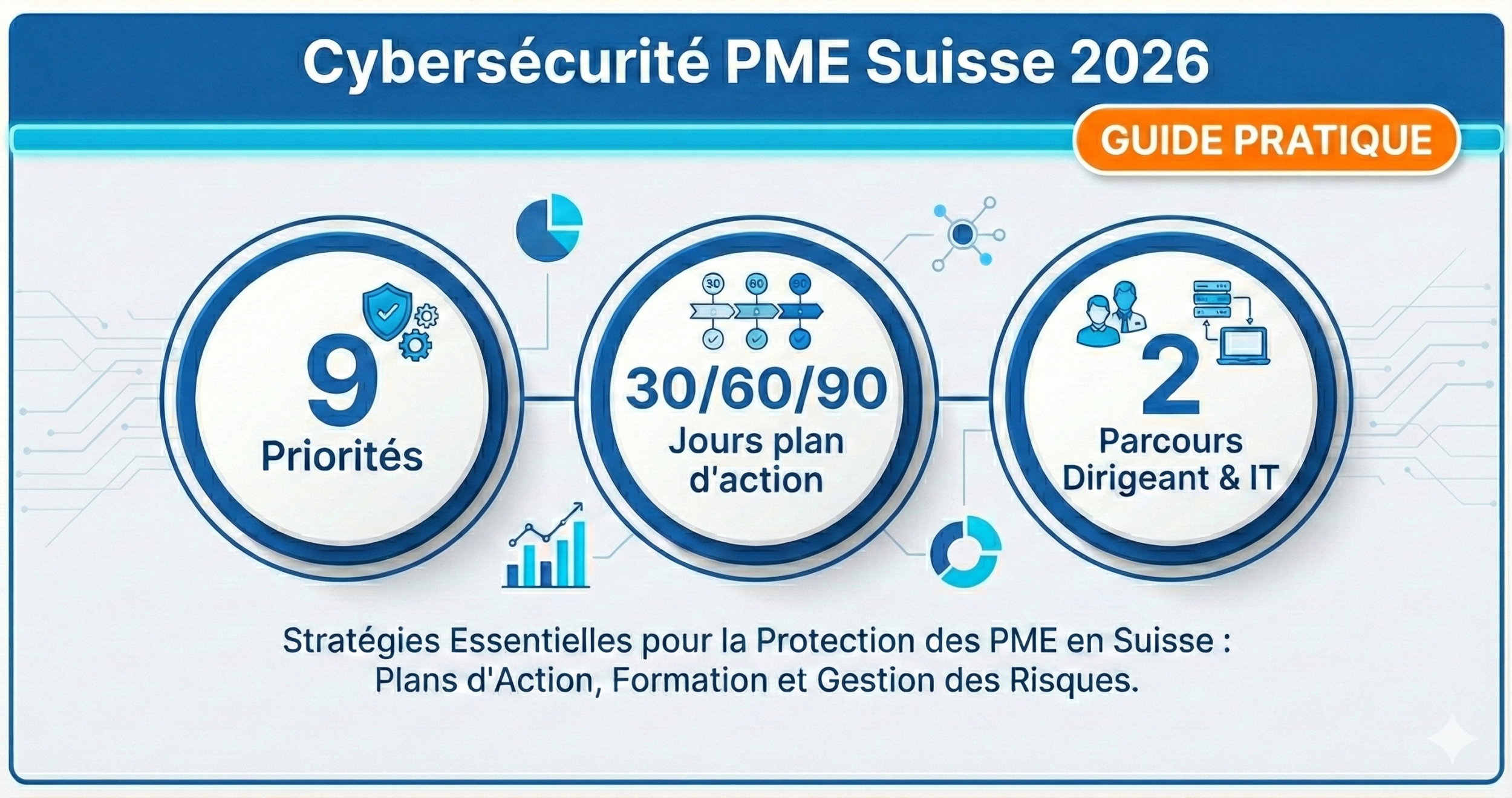
Complete Shadow IT / Shadow AI guide for Swiss SMEs: nLPD risks, Cloud Act, sovereign solutions (Euria, kDrive, Proton Drive, SwissTransfer) and practical governance.